Setting Up DUO with RADIUS
Users prefer Pleasant Password Server with a KeePass client!
Password Server supports authenticating with DUO with a RADIUS proxy as a Two-Factor Provider, and allows use of the DUO Push technology.
Applies to:
- Versions 7.11.28+
Prerequisite:
- DUO configuration steps
Configure DUO
Download DUO proxy
- For example, download DUO Authentication proxy from here:
Modify the Config File
- C:\Program Files\Duo Security Authentication Proxy\conf\authproxy.cfg
[duo_only_client]
[radius_server_duo_only]
ikey=[FROMDUO]
skey=[FROMDUO]
api_host=[FROMDUO]
failmode=safe
radius_ip_1=[PASSWORD SERVER IP ADDRESS]
client=duo_only_client
radius_secret_1=MyLongSecret123
port=1812
Password Server Configuration
- Users are able to authenticate through a single-step logon procedure able to output text into a web form. For example, a static password or most One-Time Password (OTP) Providers will be sufficient.
-
Users with the same username in Password Server as they have in DUO. This will likely be the case if both Password Server and DUO are importing from the same LDAP server.
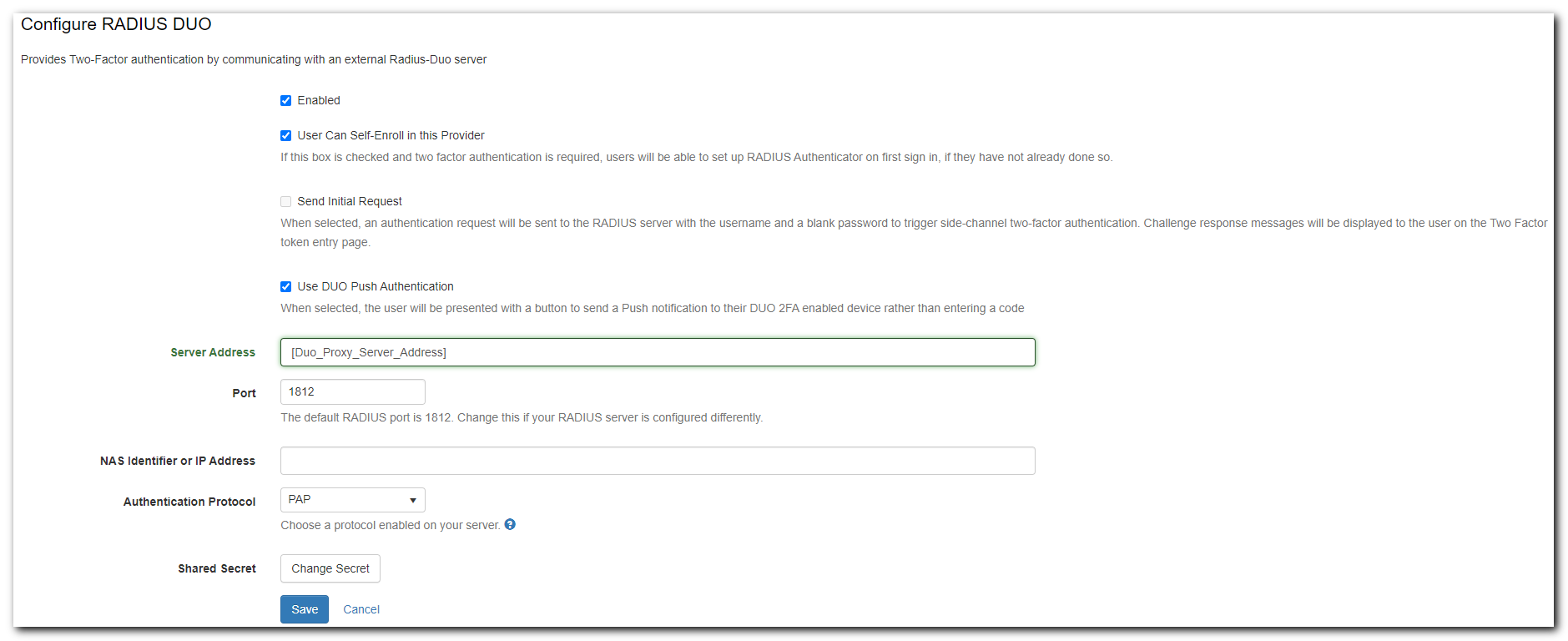
In Password Server itself, the configuration is simple.
- Go to Users and Roles > Manage Policies and click the name of the user policy containing the users you want to authenticate against RADIUS-DUO.
- Scroll down to Two Factor Policy and look for RADIUS-DUO in the configuration list. Click the [Configure] link in that row.
- Using the details required by RSA SecurID, fill in the fields:
- Set Enabled to True
- Set "User Can Self-Enroll in this Provider" (optional)
- Send Initial Request (cannot be checked if using DUO Push)
- Use DUO Push Authentication (must be checked for DUO Push)
- Server Address
- Server Port
- Select an Authentication Protocol - enabled for RSA SecurID
- See: available protocols
- Shared Secret
- Click Save.
- Server address: is the IP address of your DUO proxy server.
- Port: 1812
- NAS Identifier or IP Address: is an optional attribute. Some servers require it but if yours doesn't you can ignore it.
- Authentication Protocol: PAP
- Shared Secret: MyLongSecret123 [for example]
Attach and Enroll Users
Additional Users can be attached to this policy by either:
- Setting a Role policy: from Policies -> Set the Role Policy or Edit -> Set Policy
- Setting a User's policy: From Manage Users -> Click User name -> Edit -> Change policy
-
Setting it as the Users' default Policy: From Policies -> Edit -> Global Settings -> Set the Default Policy
Disabled: Users attached to the policy will show as disabled, until they are enabled or enrolled or self-enrolled.
Enabling 2FA for a User
Two-Factor Authentication can also be enabled individually for all users you would like to authenticate against a RADIUS server:
- Go to Users and Roles > Manage Users and click the name of the user you want to enable RADIUS for.
- Scroll down to Policy Information and look for RADIUS-DUO in the Two Factor Authentication list. Click the [Configure] link in that row.
- Click the Enable button. The user will now be prompted with a Send Push which if pressed will send a push notification to the 2FA device.
- If RADIUS-DUO needs to be disabled for a user, you can go back to the previous screen and a Disable button will be present instead of the Enable button.
User Configuration and Self-Enrollment
We now have two different workflows depending on your configuration:
Send Initial Request
The prompt for this user configuration, and subsequently, for each time they use 2FA:
-
"Please enter the one-time password or secret code."
- We can enter "sms" to have a code text messaged to your mobile phone and input that code to authenticate.
Duo Push Authentication
The prompt for this user configuration, and subsequently, for each time they use 2FA:
-
"Send Push"
Configuration error:
-
"RADIUS configuration failed. Please try again"
Token entry error:
-
"Invalid two-factor token. Please try again"
Using RADIUS via Duo
The support documentation on Duo's website has instructions for setting up the Duo proxy service as a RADIUS server or client.
- Be sure to follow the above instructions until the "start the proxy" step.
Setup Requirement: The only requirement for using this setup with Password Server is that PAP must be selected as the authentication protocol in the policy configuration.
When a user logs in, they must type in both their password and Duo token as described in Duo's documentation here. If you are using the Duo-only client, this is unnecessary; users just need to type in their Duo token to authenticate.